GeoComply Core
Get compliance-grade geolocation that also helps stop fraud
Onboard more legitimate customers, fight fraud, and optimize revenue.
*Based on historical performance.
Build a better business with a better system
We’ve worked through billions of transactions over the last decade to land at the best system. We’re constantly updating our software according to the latest fraud and compliance trends to keep you ahead of risk.
Comply with location-based requirements
Jurisdictional compliance is all about location. GeoComply Core pinpoints a customer’s location to within meters, to accurately determine if they’re in a sanctioned country or a restricted jurisdiction.
Understand the risk of every online interaction
Location spoofing and device tampering may indicate a malicious actor at work. GeoComply Core runs hundreds of location data, device integrity, and identity fraud checks on every geolocation transaction to detect suspicious activity.
One dashboard, endless insights
Analyze your geolocation transactions to get quick snapshots and detailed analysis of your top fraud risks. Zoom in on fraud hotspots with precise geofencing, and improve customer support with enhanced troubleshooter messages and updated FAQs.
Device-agnostic, complete security
Supports all environments, including SDKs for desktop, mobile apps, and web browsers. End-to-end encryption secures customer data and deters malicious hackers.
Historical risk engine
Sophisticated machine learning assesses billions of historical transactions and fraud hotspots, to constantly update existing rules against new threats.
Device integrity and intelligence
Analyzes all forms of fraudulent device activity such as jailbroken devices, fake location apps and emulators.
User integrity and intelligence
Protects against fraudulent activities associated with users such as location jumping, proxy betting, account sharing and account takeover.
Location intelligence
Combines all geolocation signals available, such as WiFi, GPS and GSM, with existing technology to augment the value of location data.
Data integrity
Identifies sophisticated location spoofing methods such as VPNs, data centers, anonymizers, proxies, Tor exit nodes, remote desktop detection, WiFi emulators, and GPS spoofing.
Performance and reliability
Processes 1.2 billion geolocation checks monthly with exceptional availability. Includes an added layer of resilience with Carbon, your fully independent failover solution.
Technical Specifications
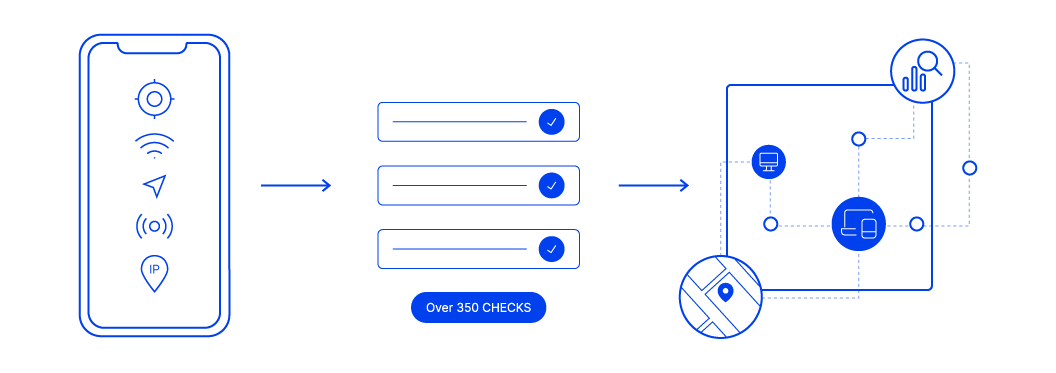
1. Collect data from a user’s device: GPS, GSM, WiFi, plus IP addresses.
2. Verify location accuracy. Our rules engine runs hundreds of location data, device integrity, and identity fraud checks on every geolocation transaction to detect suspicious activity.
3. Combine real-time and historical data to detect and flag patterns of location fraud. Our models are constantly updated with the use of machine learning and human intelligence.